Cybersecurity Insights & Expertise
Stay ahead of evolving threats with expert analysis, industry trends, and practical cybersecurity guidance from our team of security professionals.
Featured Article
 Featured
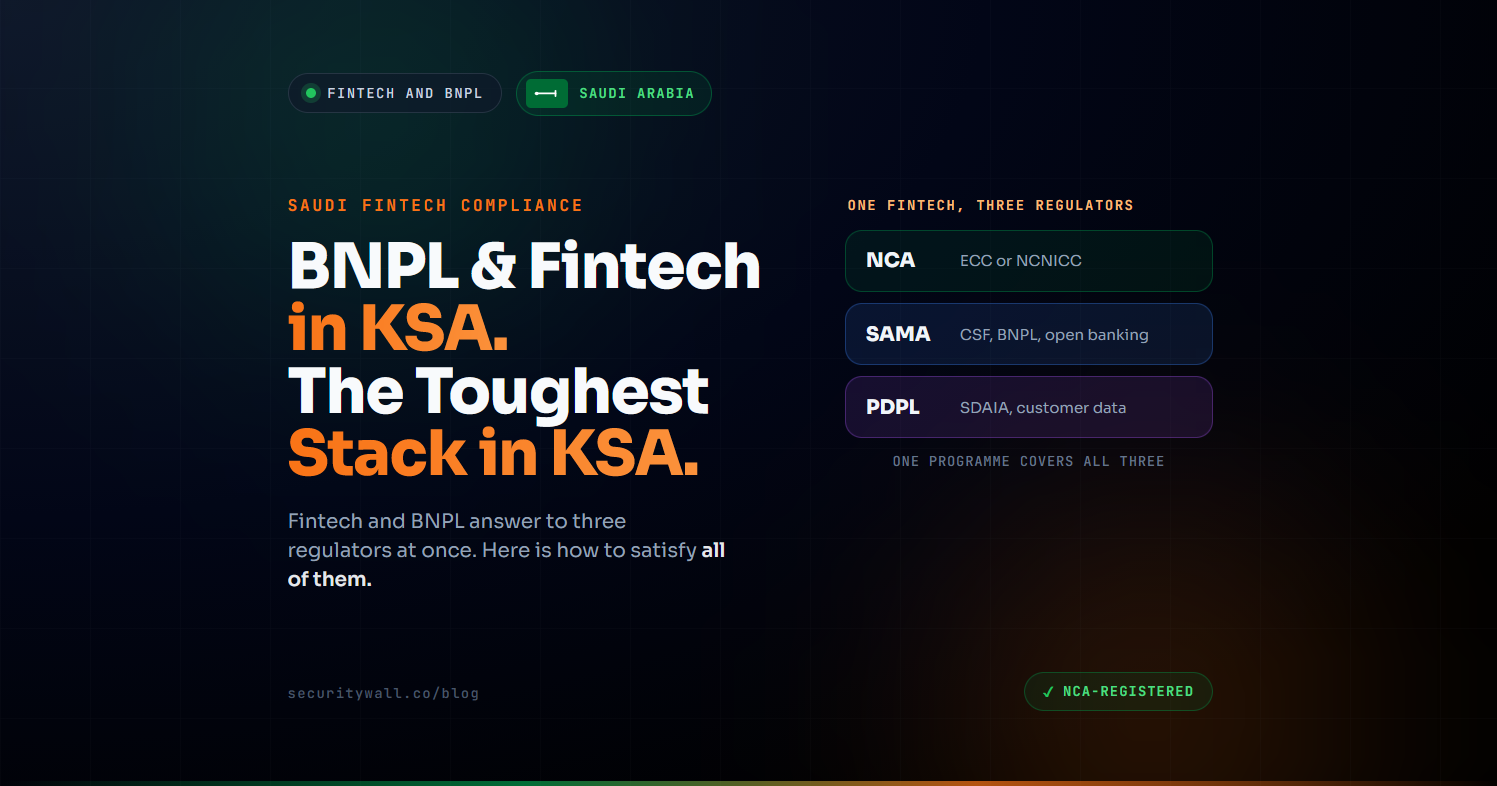
FeaturedNCA Compliance for Fintech and BNPL in Saudi Arabia
A Saudi fintech does not answer to one regulator. It answers to three. SAMA licenses and supervises it, the NCA mandates its cybersecurity controls, and the Personal Data Protection Law governs how it handles customer data each with its own requirements, its own assessments, and its own consequences for getting it wrong. No other sector in the Kingdom carries a compliance stack this dense, and few founders realise it until they are mid-launch. For buy-now-pay-later companies, it is sharper stil
Hisham Mir
Jun 3, 2026
Latest Articles
Showing 1-12 of 96 articles
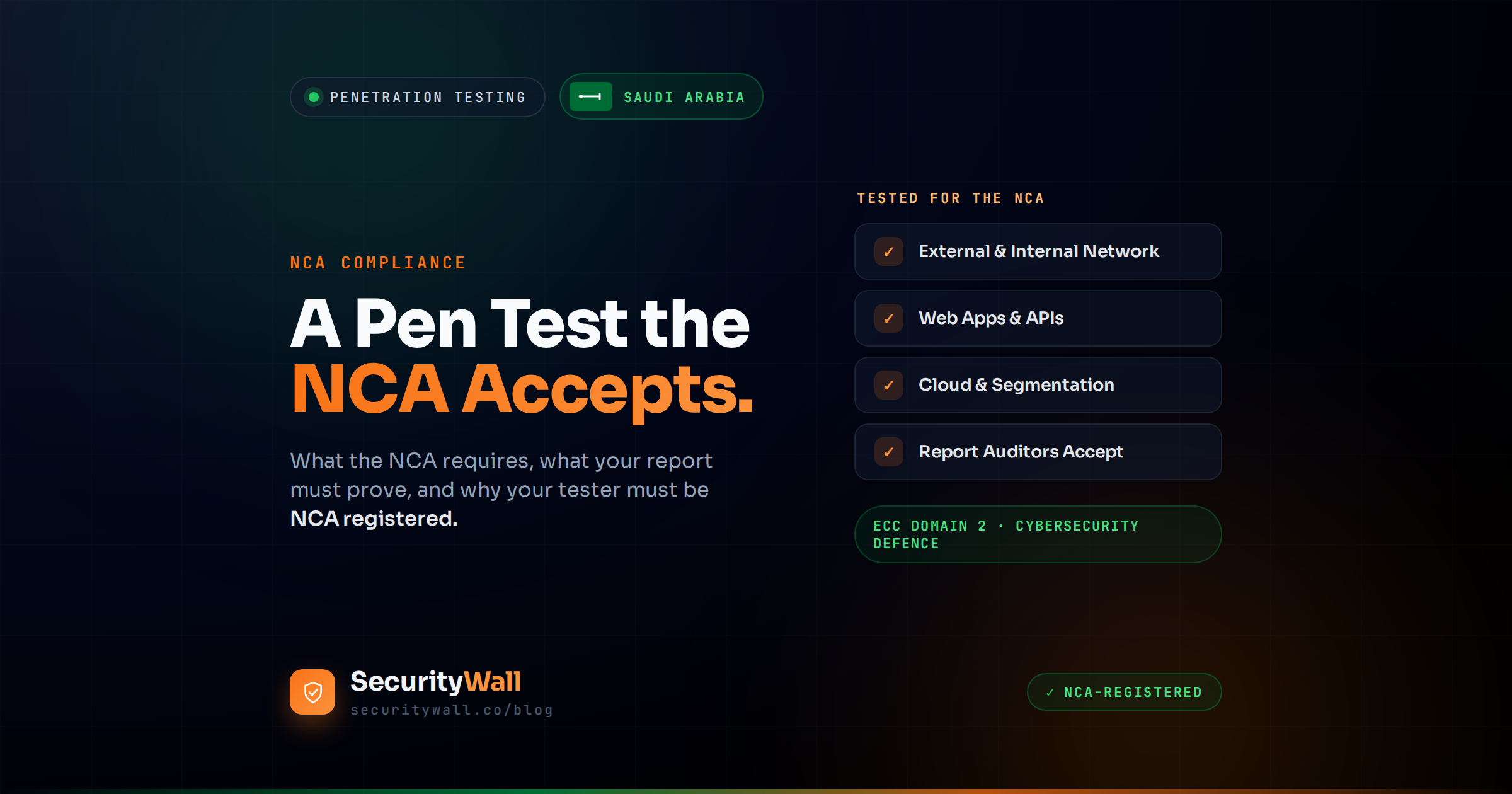
NCA Penetration Testing Requirements in Saudi Arabia
If you are reading this, you are probably close to a decision: your organisation needs penetration testing for NCA compliance, and you need to know exactly what the regulator expects, what your report has to contain, and who is actually allowed to do the testing in Saudi Arabia. This guide answers all three. But if you're still into "What is NCA Saudi Arabia?" we have the guide available. The short version is that yes, the NCA requires penetration testing it is a specific control within the NCA
Babar Khan Akhunzada
Jun 2, 2026
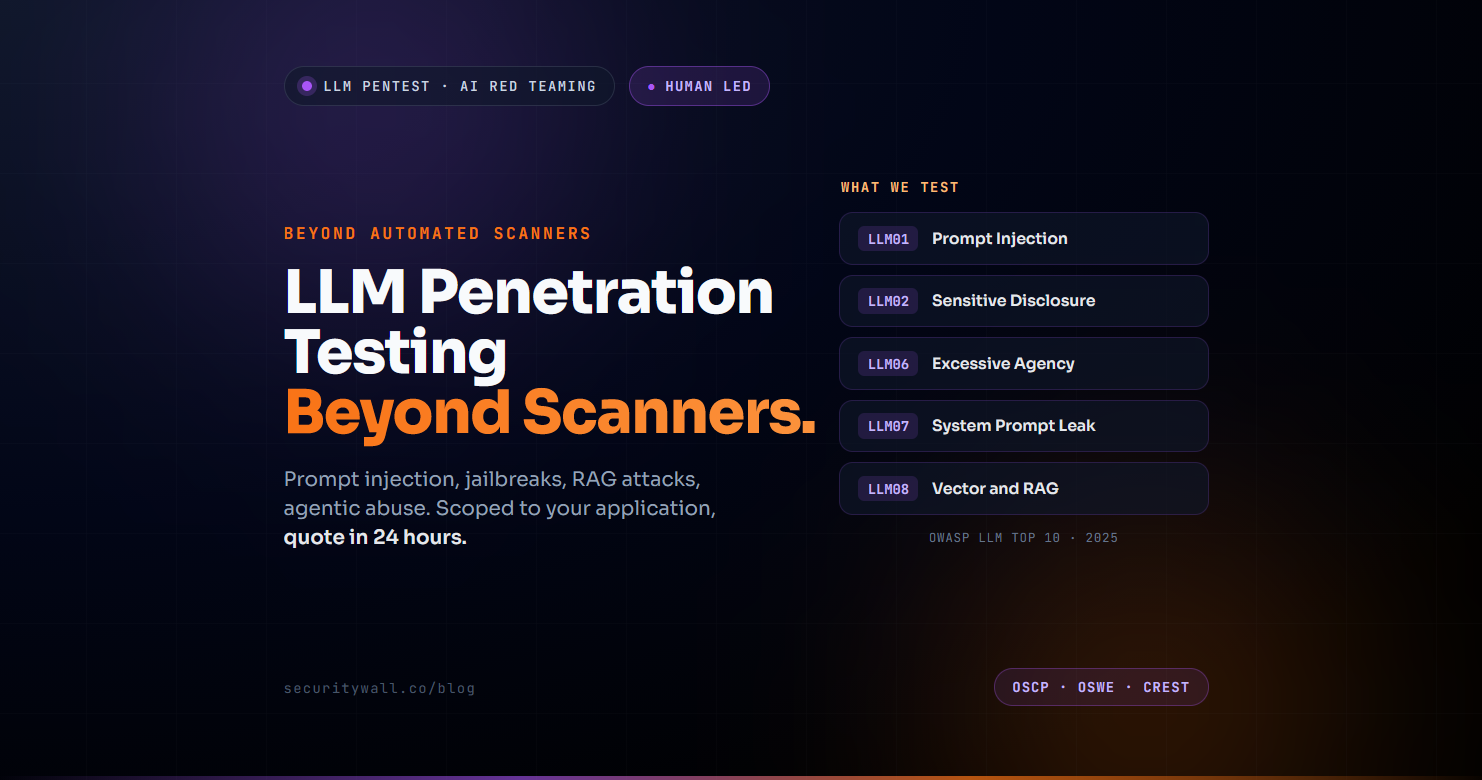
LLM Penetration Testing: How to Test AI Applications
LLM applications shipped fast, mostly without a security review, and the attack surface has been catching up ever since. Prompt injection now sits at the top of OWASP's LLM Top 10 for the second consecutive year. Agentic systems with the ability to call functions, browse the web, and execute code in autonomous loops have expanded the blast radius from "the model says something embarrassing" to "the model exfiltrates production data and triggers downstream actions." Vector databases and RAG pipel
Babar Khan Akhunzada
May 31, 2026
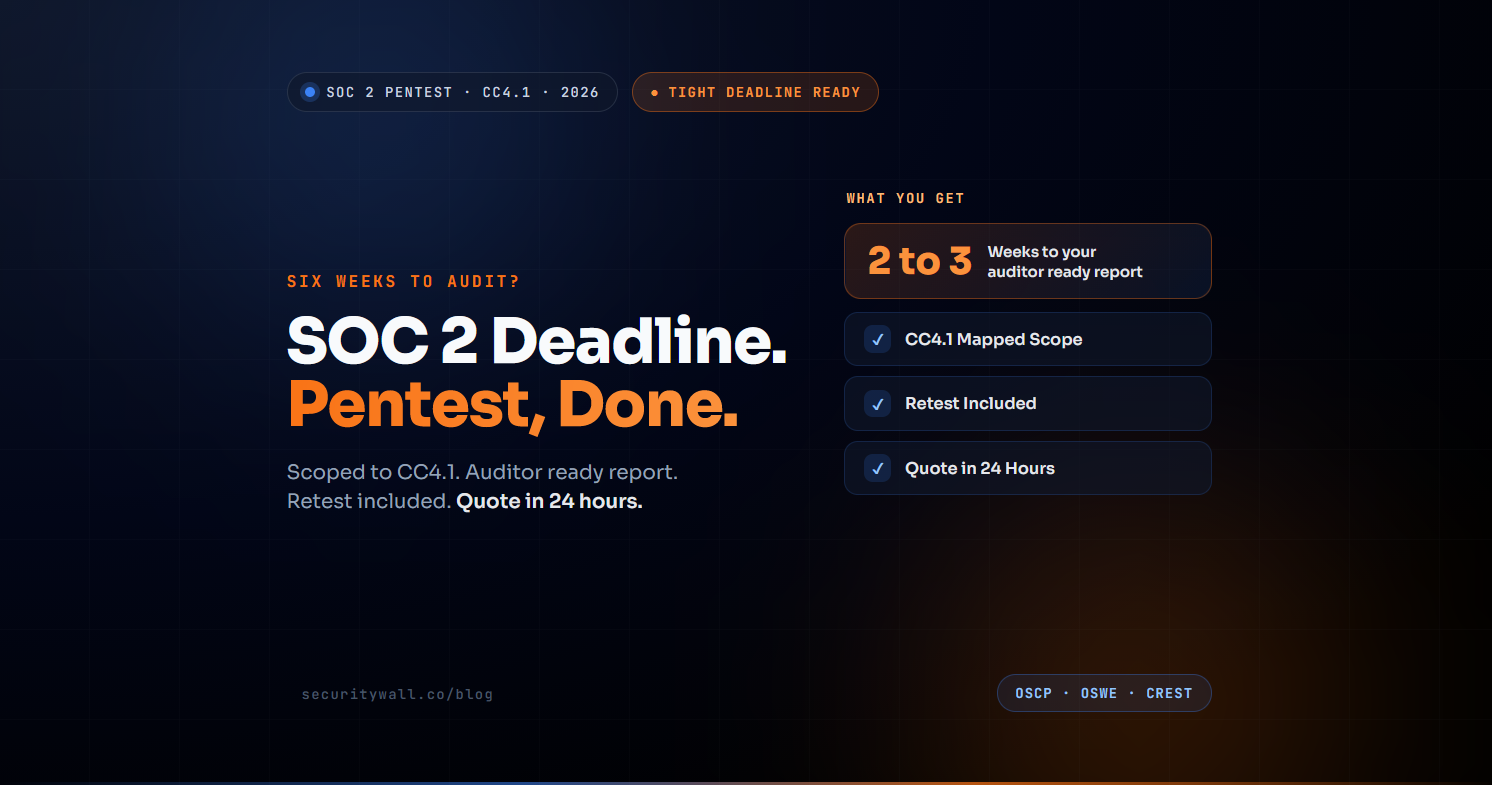
SOC 2 Penetration Testing: Requirements, Cost and Timeline
You have a SOC 2 audit on the calendar. Your auditor has told you a penetration test will need to be part of the evidence file, and now you have somewhere between four and twelve weeks to make it happen alongside everything else in the run-up to the audit window. The questions that surface in the next few hours look something like this: does SOC 2 actually require a pentest, what does it need to cover, how long does one take, how much will it cost, and can you somehow combine it with the SOC 2 r
Hisham Mir
May 31, 2026
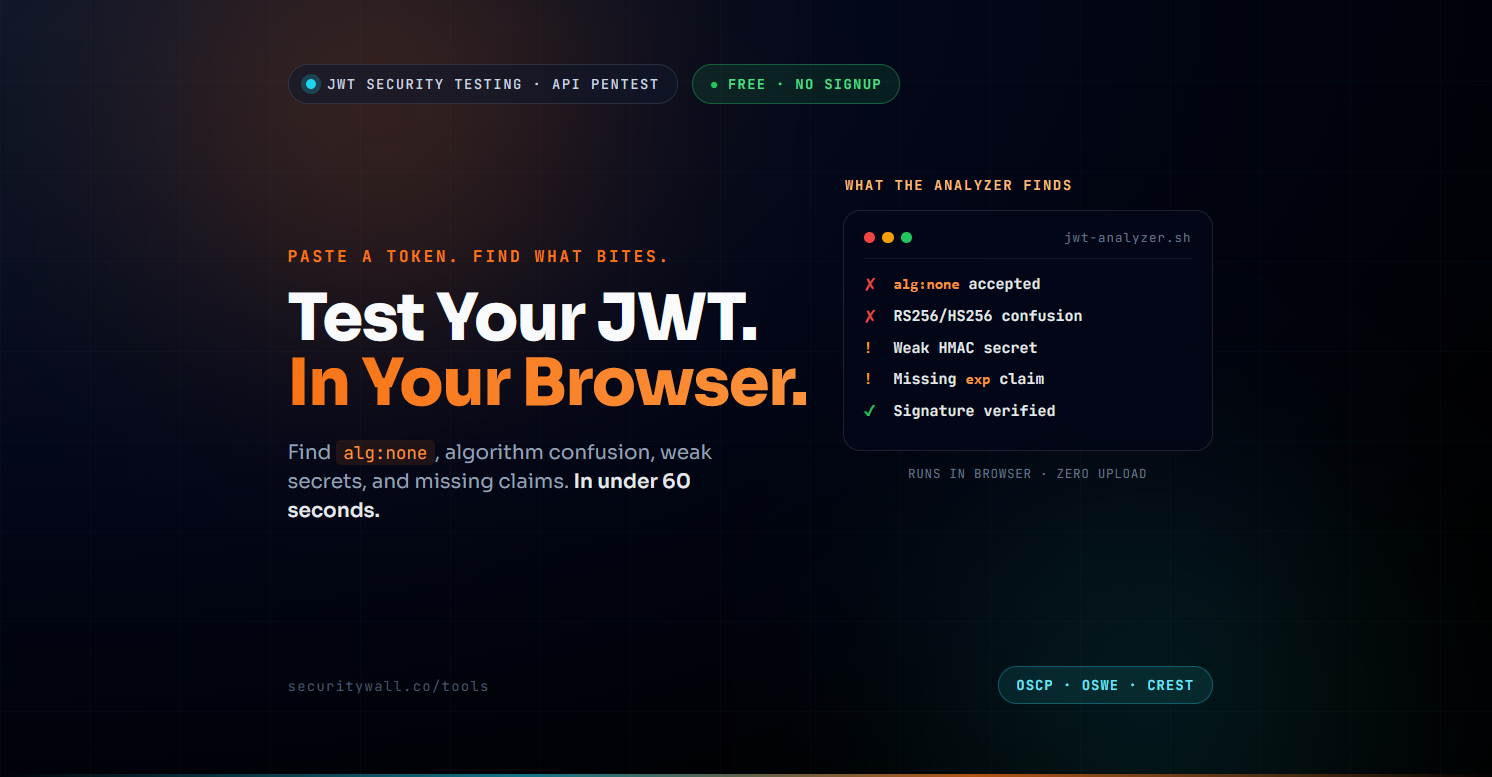
JWT Security Testing: Use the Free JWT Analyzer
JSON Web Tokens are everywhere every modern API, every SaaS authentication flow, every microservice handshake and the same handful of JWT vulnerability classes have been exploited in real-world breaches for the better part of a decade. The reason they keep working: most teams treat JWTs as "just a string we pass around" and never look closely at the algorithm, the secret, the claims, or the library's handling of edge cases until something breaks. SecurityWall's free JWT Analyzer runs in your br
Hamza Razzaq
May 31, 2026
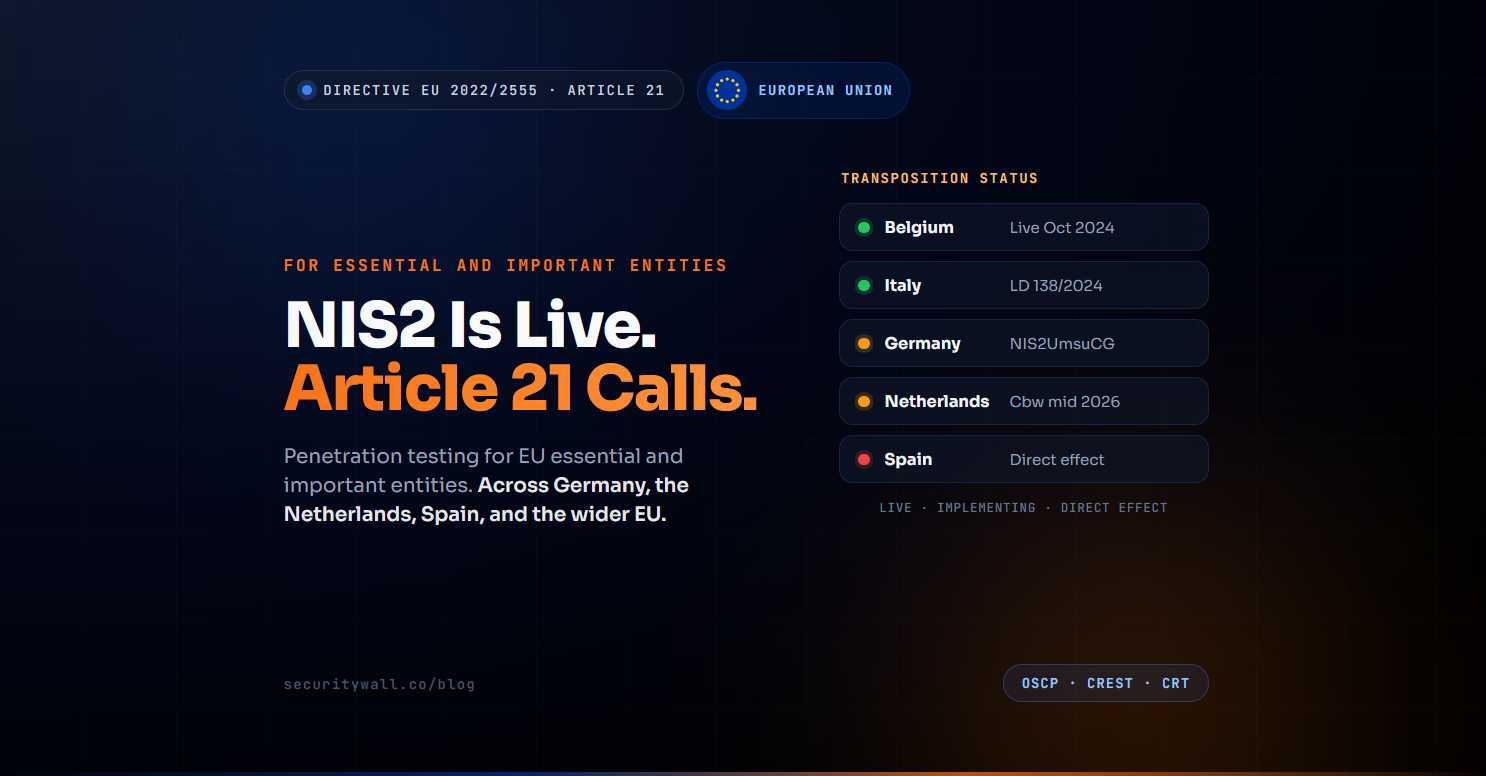
NIS2 Penetration Testing Requirements
If you are reading this, the news has already reached you: NIS2 is in force, your organisation falls within scope, and one of the obligations being interpreted across every member state is regular penetration testing. The Directive itself never says the words "penetration test" but Article 21(2)(f) requires "policies and procedures to assess the effectiveness of cybersecurity risk-management measures," and across the EU's regulators, supervisors, and consultancies that requirement is being treat
Hisham Mir
May 31, 2026
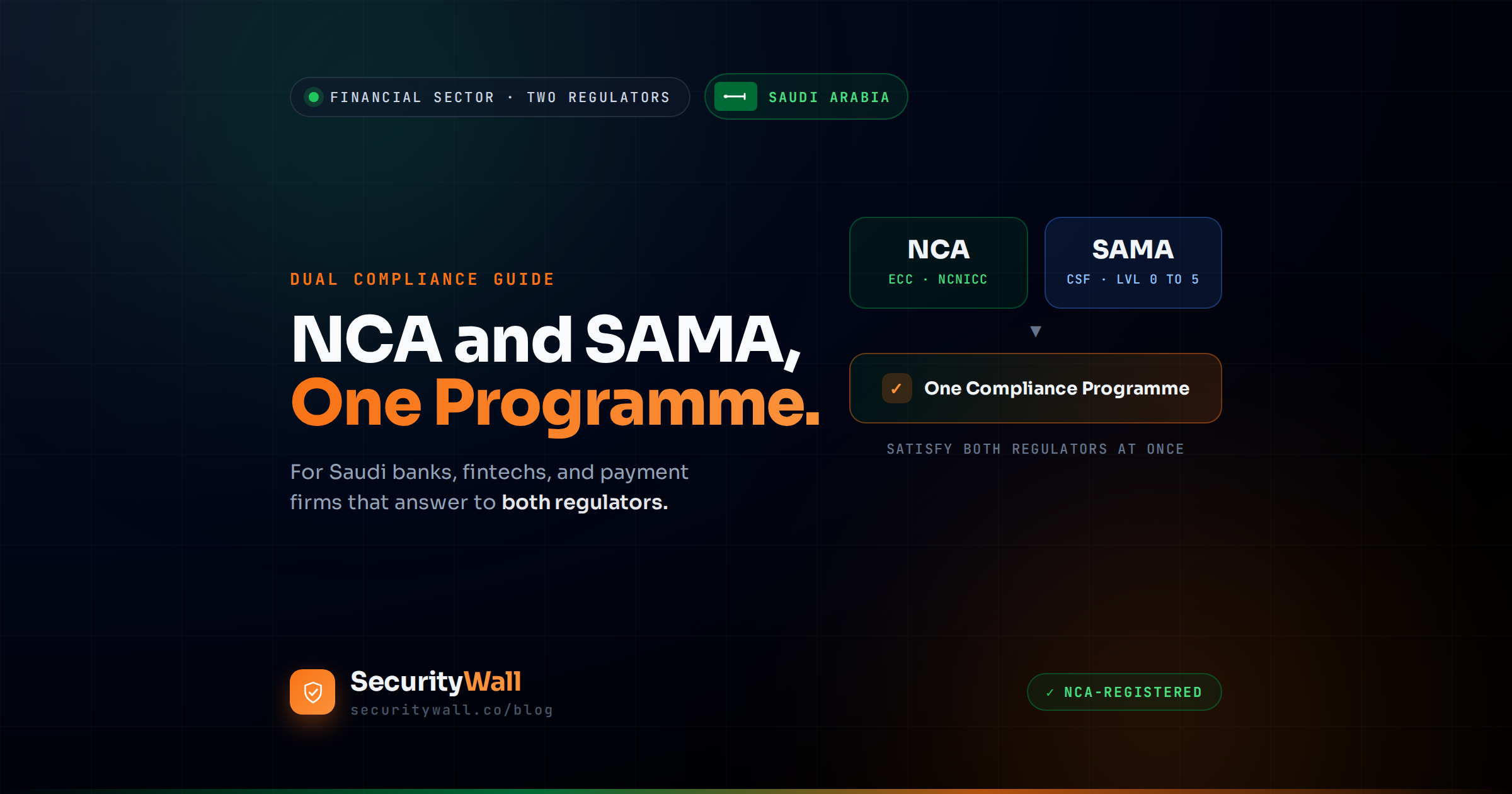
NCA and SAMA Dual Compliance for Banks and Fintech
Most Saudi financial institutions discover the problem the same way: they finish a SAMA compliance programme, feel done, and then learn the National Cybersecurity Authority has its own mandatory requirements they have not touched. Or the reverse they treat the NCA's controls as the whole job and miss the maturity-level evidence SAMA's supervisors expect. SecurityWall NCA ECC Checklist and SAMA Compliance Checklist can assist you with initial vetting. If you are a bank, fintech, payment company,
Hisham Mir
May 30, 2026
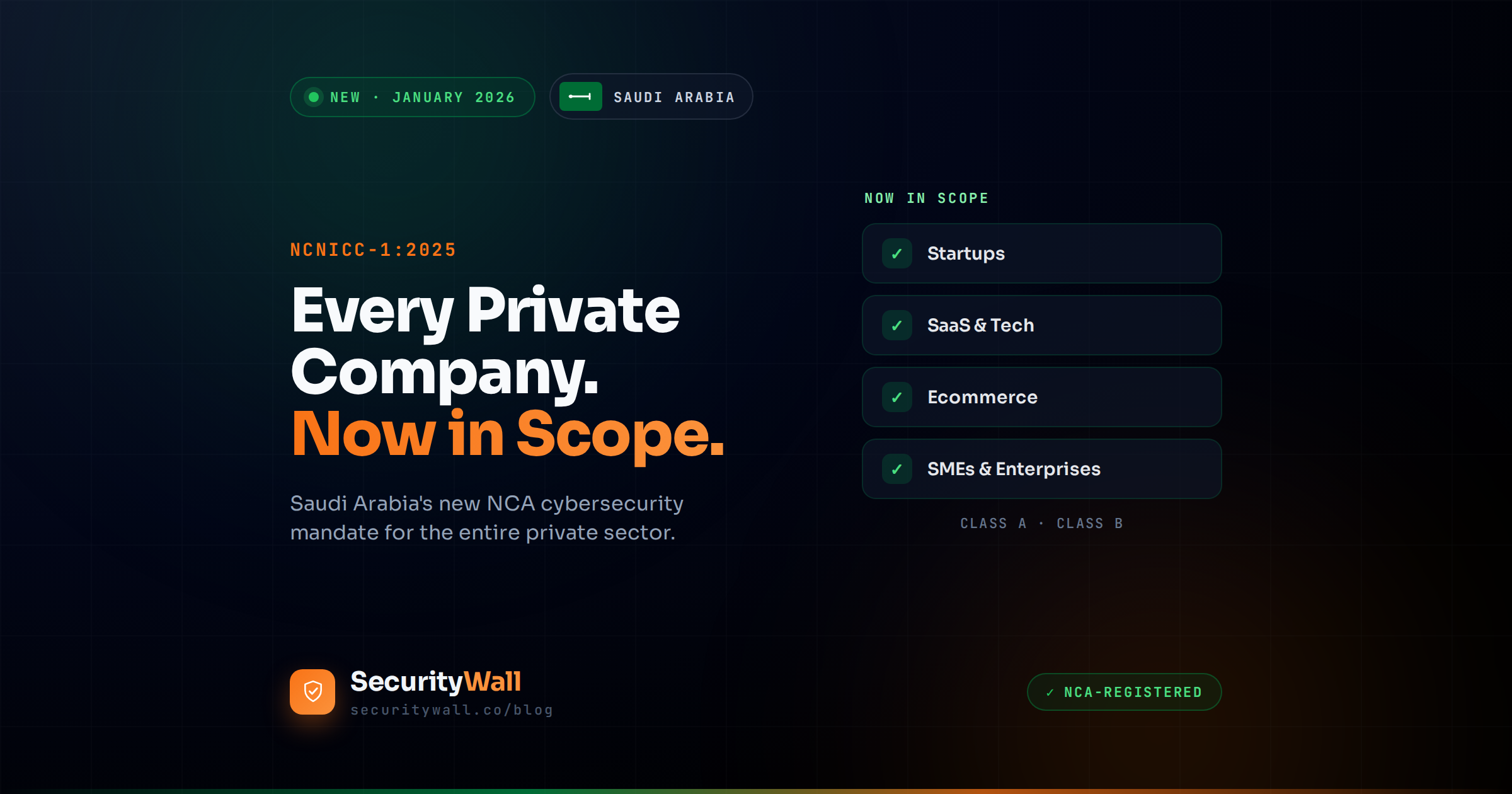
NCNICC-1:2025: Every Saudi Private Company Now in Scope
For years, Saudi Arabia's cybersecurity regulations were something most private companies could safely ignore. The National Cybersecurity Authority's rules applied to government bodies and operators of Critical National Infrastructure banks, energy, telecoms and almost everyone else watched from the sidelines. In January 2026, that changed completely, and most companies still do not know it. If you are ready for compliance we have NCA ECC Checklist: Score Your Readiness, No Sign-Up. The NCA rel
Hisham Mir
May 28, 2026
SOC 2 Compliance for SaaS: The Complete Guide
There is a moment almost every B2B SaaS company hits. A major enterprise deal is moving, an investor is circling, or a regulated customer enters procurement and then the email arrives: "Please share your SOC 2 report." If you do not have one, the deal stalls, sometimes for months, sometimes for good. SOC 2 has quietly become the price of entry for selling software to serious customers. SOC 2 compliance for SaaS means having an independent auditor attest, in a formal report, that your company's
Hisham Mir
May 25, 2026

NCA ECC Checklist: Score Your Readiness, No Sign-Up
NCA ECC Compliance Checklist
Babar Khan Akhunzada
May 25, 2026
NCA ECC: 4 Domains, 108 Controls & Compliance Explained
If you are reading about the NCA's Essential Cybersecurity Controls, there is a good chance the guidance in front of you is out of date. Most articles still describe ECC-1:2018 the original version including its control count, its five domains, and its Saudization rule. All three of those changed when the NCA released ECC-2:2024, the NCA ECC Checklist: Score Your Readiness in Saudi Arabia. The Essential Cybersecurity Controls are the NCA's foundational framework: the minimum cybersecurity requi
Hisham Mir
May 25, 2026

What Is the NCA? Saudi Arabia's Cybersecurity Authority
If you run a business in Saudi Arabia, the rules on cybersecurity changed at the start of 2026 and the change now reaches far more companies than before. The body behind those rules is the National Cybersecurity Authority, almost always referred to simply as the NCA. SecurityWall offers NCA ECC Checklist: Score Your Readiness, No Sign-Up. The NCA is Saudi Arabia's national cybersecurity regulator the single government authority responsible for setting, issuing, and enforcing cybersecurity requi
Hisham Mir
May 24, 2026

SOC 2 Compliance Checklist 2026 (Interactive, 12 Domains)
This is an interactive, use-it-now SOC 2 compliance checklist covering all 12 control domains. Tick items as you go the progress bar tracks your completion, and each domain tells you exactly what evidence auditors look for and the single most common gap they find. Nothing is saved or sent anywhere; it runs entirely in your browser. The checklist gives you the shape of SOC 2 readiness the key checkpoints in each domain. It is not the full control set; a complete SOC 2 programme spans 200+ contro
Hisham Mir
May 24, 2026