Cyber Security Prediction for 2019 - Threat Intelligence
Hisham Mir
December 2, 2018
Cybersecurity Threat Predictions for 2019: Article include brief about prediction from different firms. Including Fortinet,McAfee,and FlashPoint.
Cyber Security can't be ignored anywhere but 2019 predicts too much, Yes! expect credit card, data, theft to continue to rise. Yes, this isn’t a major surprise; however, if organizations can better address the reasons for the rise, they will be better for the journey in 2019.
Cyber criminals are expected to become more sophisticated and collaborative.
Experts looking at 2019 cyber security environment are predicting that the attacks which are generated through social engineering may get more advance techniques and new approach to break into victims. McAfee also shared a scenario in their recent 2019 prediction report where a simple phishing mail can lead to ransomware or a cryptocurrency miner.
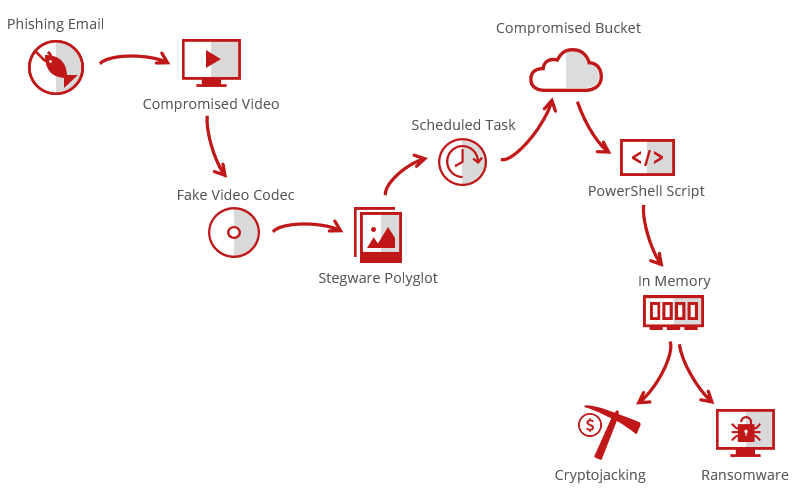
The attack raises many questions: What are you dealing with? Is it phishing 2.0? Is it stegware? Is it fileless and “living off the land”? Cryptojacking? Ransomware? It is everything at the same time.
“Additionally next-gen” teams will dominate. That is, security teams will start using more technologies to achieve detection and response versus simply relying on the compliance alone. Deploying more and more technologies is not enough. In 2019, organizations will need to work with employees on their cyber security understanding as well and should not only take care of System, Network, Application but social engineering is now evolving and special attention is required.
Organization CEO's and CTO's should decide now including preventing revenue loss due to fraud and brand infringement, detecting and mitigating attacks before they enter the companies or to Pentest after a breach. Application based (web or mobile apps) companies should take it more seriously as in past many companies were breached due to application layer vulnerabilities and effecting whole network.
Companies need to :
- Go beyond automated detection complaisance and SOC's
- Do focus on collection capabilities, orchestration, and automation, which can demonstrate ROI very quickly.
- Adopt Managed Detection and Response operations that are more focused on advanced threats and compliance than the SIEM.
- Prepare for more sophisticated tools, tactics
- Give time to real-time monitoring and response
- Ready for advance script-based malware
- Focusing on cyber security along with digitization.
FlashPoint also published their own prediction report, where they concluded on national and state level cyber threats.
Threat actors are ranked on a six-point capability scale and a four-point potential impact scale, with Flashpoint's cast ranging from Tier 2 capability/Negligible potential impact (Jihadi hackers) to Tier 6/Catastrophic impact (China, Russia and Five Eyes).
It's probably no surprise to find China heading the 2017/18 ranking of threat actors, in terms of capability, potential impact and number of verticals targeted:
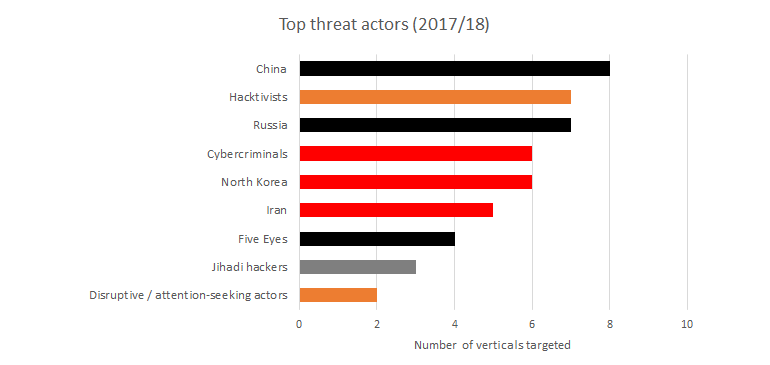
Colour coding corresponds to Flashpoint's 'potential impact' rating (Black = Catastrophic).
Data: Flashpoint / Chart: ZDNet
Next step: Organizations who have reached “security maturity” don’t just need to monitor, they also need to detect, respond and, most of all, manage, i.e., orchestrate and automate all the threat alerts, intelligence, mitigation, and response. According to Enterprise Strategy Group research, just 19% of enterprises have now deployed security automation and orchestration technologies extensively. Has your organization begun?
Finally, researchers predict there will be a significant increase in data exfiltration attacks that target the cloud. Because of an increase in users collaborating on this data, hackers are using numerous methods to seek more targets, especially those with weak application program interfaces (APIs) or ungoverned API points. As mentioned above, automated products may not help you to defend against sophisticated and silent penetrations. Web and Mobile application is a key target for those attackers to focus and find vulnerabilities instead of attacking on your main network. Secure it before you lose it.
Preparing for 2019? Stay ahead of threats — reach out to us at securitywall.co/contact
Tags
About Hisham Mir
Hisham Mir is a cybersecurity professional with 10+ years of hands-on experience and Co-Founder & CTO of SecurityWall. He leads real-world penetration testing and vulnerability research, and is an experienced bug bounty hunter.