In-House SOC vs Managed Security Services: Full Comparison 2026
Hamza Razzaq
February 18, 2026
The question is no longer whether your organization needs a Security Operations Center (SOC). The real decision is how to operate one without overspending, overworking your analysts, or under-protecting your business.
Across the US, UAE, Germany, Spain, Saudi Arabia, and Qatar, security leaders are reassessing the traditional in-house SOC model. Rising labor costs, cloud complexity, compliance pressure, and 24/7 attack surfaces are pushing organizations toward Managed SOC Services or structured hybrid approaches.
This guide breaks down:
- In-House SOC vs Managed SOC Services
- SOC services pricing and realistic 3-year TCO
- Control, customization, and data residency concerns
- Regional comparisons (UAE, US, Germany, Spain, Saudi Arabia, Qatar)
- A final decision framework for founders, CISOs, and IT leaders
If you're still evaluating fundamentals, start with our Security Operations Center Guide or request a Free Security Operations Center Assessment to benchmark your current maturity.
In-House SOC vs Managed SOC: Direct Comparison
| Factor | In-House SOC | ⚡ Managed SOC | Hybrid |
|---|---|---|---|
| 24/7 coverage | ✕ Requires 8–12 analysts minimum | ✓ Included from day one | ✓ Provider covers off-hours |
| Time to operational | 6–18 months | 2–6 weeks | 4–8 weeks |
| 3-year cost (mid-market) | $3M – $6M+ | $300K – $900K | $600K – $1.5M |
| Control & governance | ✓ Full ownership | ◑ Governance retained, execution delegated | ✓ Full internal governance |
| Detection tuning | ◑ Dependent on team bandwidth | ✓ Continuous, dedicated engineers | ✓ Provider-led with internal oversight |
| Talent retention risk | High — Tier 1 churns 12–18 months | None — provider absorbs risk | Low — small internal team |
| Compliance reporting | ◑ Manual — requires dedicated effort | ✓ Automated, audit-ready output | ✓ Provider handles reporting layer |
| Best for | 10,000+ endpoints, $2M+ budget | Startups to mid-market, growth-stage | Mid-market needing governance + scale |
|
Not sure which model fits your stage and budget? Get a Free SOC Assessment → |
|||
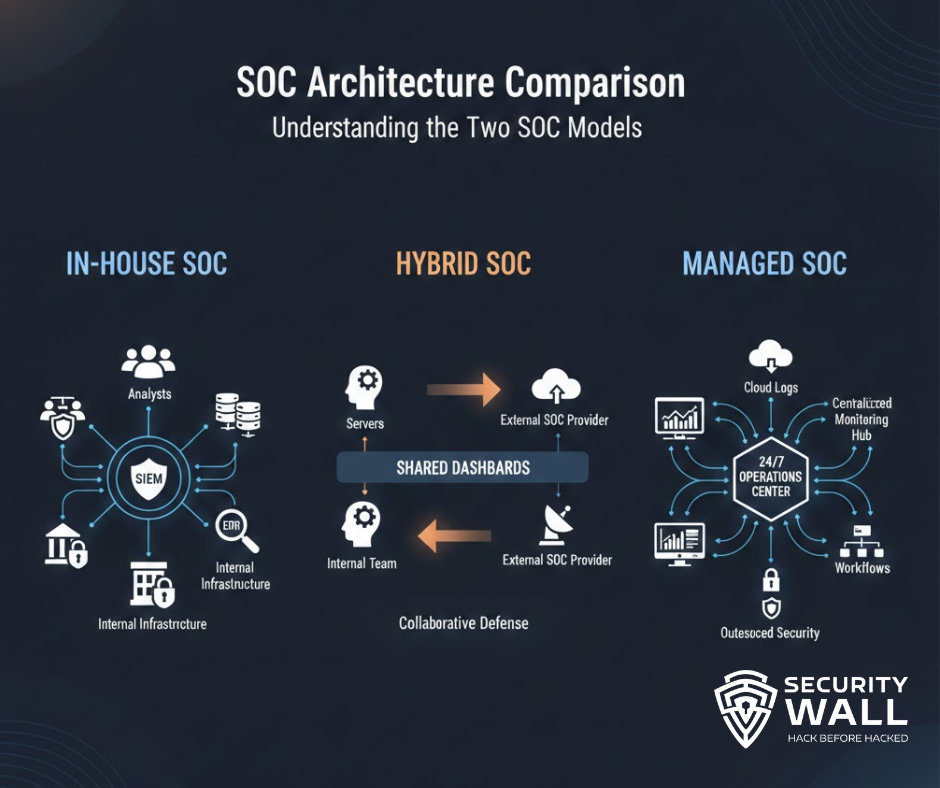
What Is an In-House SOC?
An in-house SOC is a security operations capability built, staffed, and managed internally.
A typical mid-market structure includes:
- Tier 1 Analysts (alert triage)
- Tier 2 Analysts (incident investigation)
- Tier 3 Analysts / Detection Engineers
- Threat Intelligence Analyst
- SOC Manager
Organizations retain control over:
- Tooling (SIEM, EDR, SOAR)
- Infrastructure and log storage
- Detection logic
- Incident response workflows
If you’re considering this route, review our implementation roadmap in the Build a SOC Step-by-Step Guide.
Building a SOC is achievable. Sustaining one at high performance is where complexity emerges.
Talk to a Security Operations Center (SOC) Expert
Before a Hacker Breach Happens
What Are Managed SOC Services?
Managed SOC Services provide 24/7 monitoring, detection engineering, and incident response through a specialized provider.
Modern managed SOC models include:
- Continuous monitoring
- Detection tuning and optimization
- Threat intelligence integration
- SOAR automation
- Compliance-aligned reporting
- SLA-backed escalation
We’ve covered the operational depth of structured security operations in our guide to SOC Monitoring and Management, and our SOC Services are designed to deliver enterprise-grade monitoring tailored for startups and mid-sized businesses.
1. The Cybersecurity Talent Shortage
The global shortage of skilled cybersecurity analysts continues to widen.
In 2026:
- Tier 1 analysts often churn within 12–18 months
- Tier 2 and Tier 3 engineers command premium salaries
- Detection engineering expertise remains scarce
True 24/7 coverage requires a minimum of 8–12 analysts to avoid burnout and operational gaps.
Most mid-sized organizations underestimate the staffing math and the financial commitment required to sustain it.
2. Alert Fatigue Is an Operational Risk
Modern environments generate:
- EDR alerts
- SIEM correlations
- Cloud misconfiguration warnings
- Identity anomalies
- SaaS access alerts
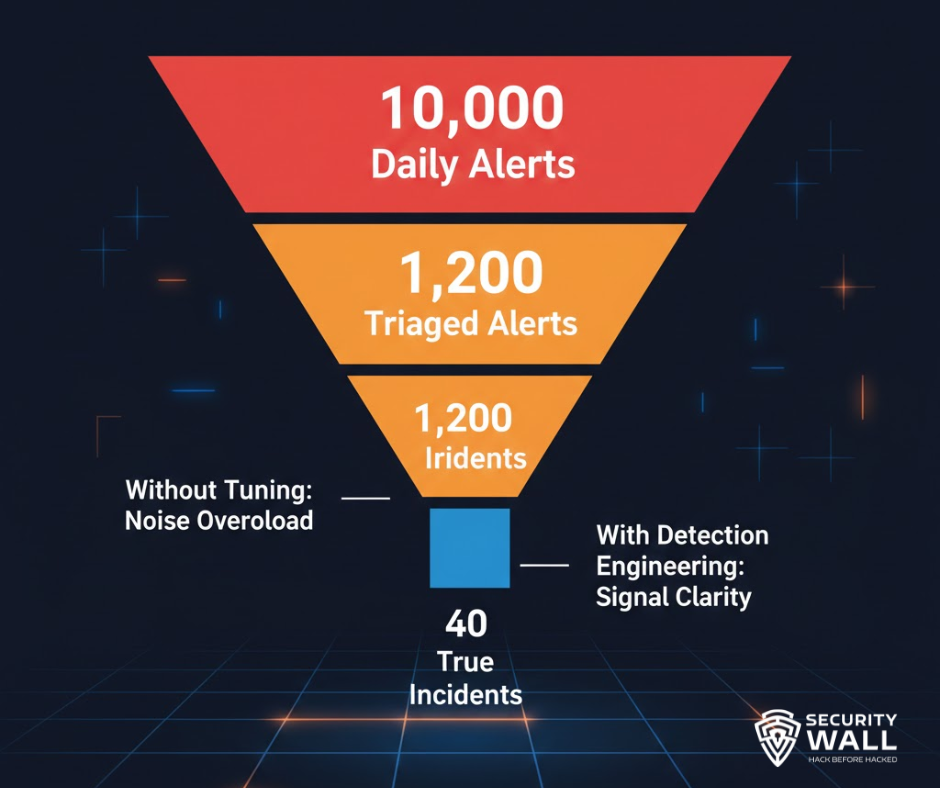
Without continuous tuning, analysts drown in noise.
Alert fatigue leads to:
- Missed high-severity incidents
- Slower response times
- Analyst burnout
- Increased turnover
Our deep dive into Alert Fatigue in SOCs explains why this issue erodes both morale and security posture.
Alert fatigue is not a productivity issue. It is a security exposure.
Drowning in Alerts But Still Missing Critical Signals?
Reduce Noise and Improve Detection Precision
3. Cloud & Hybrid Complexity
Today’s SOC must monitor:
- AWS, Azure, GCP
- Microsoft 365 and Google Workspace
- Remote endpoints
- APIs and microservices
- Identity providers
Traditional perimeter-based monitoring models no longer apply.
AI-driven detection and SOC AI & Automation are now operational requirements, not optional enhancements.
4. The 24/7 Reality Check
If your SOC runs 9–5 with on-call escalation, you do not have continuous coverage.
Ransomware groups frequently deploy payloads during:
- Holidays
- Weekends
- Early morning hours
A coverage gap creates dwell time and dwell time creates damage.
Is Your SOC Truly 24/7 — Or Only 9–5?
Identify Monitoring Blind Spots Before Attackers Do
For startups and mid-sized enterprises, this is ultimately a capital allocation decision.
The question is rarely:
“How much does monitoring cost?”
The real question is:
“What will this decision cost us over the next three years — financially and operationally?”
Let’s model it properly.
In-House SOC Cost Breakdown
| Cost Dimension | In-House SOC Model | Strategic Implication |
|---|---|---|
| 24/7 Staffing Requirements | 8–12 Security Professionals | High payroll dependency & retention exposure |
| Annual Staffing Commitment | Multi-layer recurring overhead | Capital-intensive operating structure |
| Detection Engineering Depth | Dependent on internal expertise | Signal quality fluctuates with team maturity |
| Tool & Log Scaling | License & ingestion volatility | Costs rise as telemetry grows |
| Burnout & Turnover Risk | High in 24/7 rotations | Operational instability over time |
| SecurityWall Strategic Alternative | Engineered SOC Architecture |
Purpose-built security operations designed around your growth stage —
eliminating unnecessary staffing layers, reducing tool sprawl,
and delivering enterprise-grade detection without structural overhead.
Speak With Our SOC Architects → |
And this assumes:
- Stable hiring market
- Low attrition
- No emergency tooling expansion
- No breach-driven emergency spending
In practice, internal SOC cost tends to rise year over year due to salary inflation and log growth.
Managed SOC Services Pricing Model
Managed SOC Services convert staffing volatility into predictable operating cost.
Below is a typical engagement model for a 1,000–2,000 endpoint organization.
| Operational Dimension | Managed SOC Model | Business Advantage |
|---|---|---|
| 24/7 Monitoring | Continuous Coverage | No shift rotation burden or after-hours exposure |
| Detection Engineering | Embedded & Ongoing | Rules continuously evolve with threat landscape |
| Threat Intelligence Integration | Proactive & Global | Faster identification of emerging campaigns |
| Automation & SOAR | Standardized Workflows | Reduced analyst fatigue & improved response time |
| Scalability | Elastic Growth Model | Monitoring expands without rebuilding your SOC |
| SecurityWall Advantage | Mid-Market Engineered |
We architect SOC programs specifically for startups and growing enterprises —
optimizing telemetry, eliminating redundant tooling, and aligning detection
maturity with business scale.
Request a Strategic Consultation → |
For many startups and mid-sized enterprises, this represents a 40–60% reduction compared to sustaining an internal 24/7 SOC while often increasing detection maturity.
Through SecurityWall’s structured SOC Services, we optimize log ingestion, streamline detection engineering, and eliminate redundant tooling — bringing enterprise-grade monitoring into a cost structure aligned with growth-stage budgets.
3-Year TCO Comparison
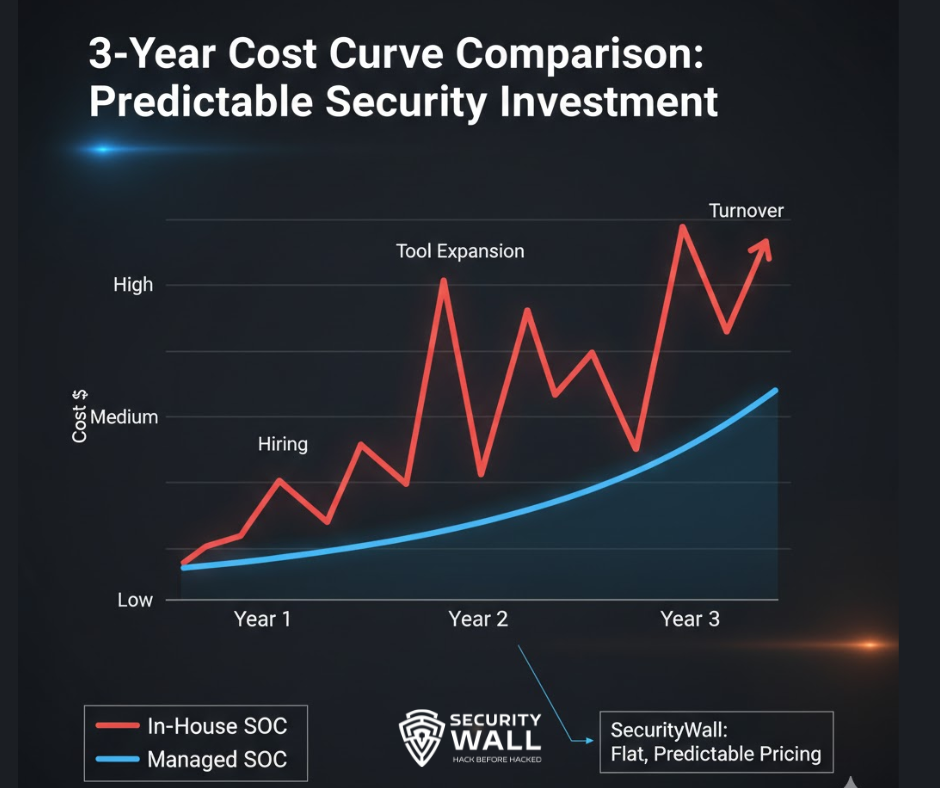
| 3-Year Strategic View | In-House SOC | SecurityWall Structured SOC |
|---|---|---|
| Capital Commitment | High Fixed Overhead | Optimized Operating Model |
| Talent Volatility | Recruitment Cycles & Retention Risk | Operational Continuity |
| Technology Efficiency | Tool Sprawl & License Expansion | Telemetry Rationalization |
| Adaptability to Threat Landscape | Dependent on Internal Bandwidth | Threat-Led & Continuously Tuned |
| Operational Stability | Vulnerable to Burnout Cycles | Institutionalized Continuity |
| SecurityWall Strategic Outcome | Ownership with Structural Drag |
Enterprise-grade detection without enterprise bloat —
engineered for growth, resilience, and long-term financial clarity.
Design Your SOC Strategy → |
For growth-stage organizations, predictability matters as much as protection. Security operations should scale with revenue not destabilize it.
Do We Lose Control?
No.
In a managed or co-managed SOC:
- You retain tool ownership (if desired)
- You approve containment actions
- You maintain dashboard visibility
- You define escalation thresholds
Execution is delegated. Governance remains internal.
What About Data Residency?
Regional compliance requirements can be addressed through:
- Geo-specific log storage
- Regional cloud deployments
- Encrypted ingestion pipelines
- Transparent architecture documentation
This is particularly critical in Germany, Saudi Arabia, UAE, and Qatar.
Can Detections Be Customized?
Yes.
Mature managed providers:
- Build custom use cases
- Continuously tune SIEM rules
- Align detections to your business risk
- Map to MITRE ATT&CK
Continuous tuning is foundational to SOC maturity.

SOC Services in UAE
The UAE’s cybersecurity spectrum is shaped by:
- NESA compliance
- DESC requirements
- Rapid digital transformation
- High cloud adoption
Due to competitive analyst salaries and limited Tier 3 availability, many UAE startups and mid-sized firms adopt managed or hybrid SOC models for sustainable 24/7 coverage.
SOC Services in Saudi Arabia
Saudi Arabia’s Vision 2030 initiatives are accelerating digitization.
Drivers include:
- NCA cybersecurity framework
- SAMA requirements
- Expansion in finance and energy
Managed SOC Services support rapid compliance alignment and scalable monitoring without extensive hiring challenges.
SOC Services in Qatar
Qatar’s financial and energy sectors face sophisticated targeting.
With a smaller local talent pool, Managed SOC Services provide immediate operational maturity and scalable 24/7 defense.
SOC Services in Germany
Germany emphasizes data sovereignty and GDPR enforcement.
Many mid-sized German companies adopt hybrid models retaining governance internally while outsourcing continuous monitoring and detection engineering.
SOC Services in Spain
Spain’s growing ransomware exposure and limited advanced detection talent have accelerated Managed SOC adoption among mid-sized organizations seeking faster maturity without major capital investment.
SOC Services in the US
In the US mid-market:
- Cyber insurance requirements demand proof of 24/7 monitoring
- SEC disclosure rules increase executive accountability
- Salary inflation strains internal SOC budgets
Managed SOC Services increasingly serve as a strategic operating model rather than a cost shortcut.
A co-managed SOC combines:
Internal Team:
- Governance
- Risk oversight
- Executive reporting
Managed Provider:
- 24/7 monitoring
- Detection tuning
- Threat intelligence
- Automation
Hybrid models are increasingly common in the US, Germany, and UAE among growth-stage organizations.
Considering a Hybrid SOC Model?
Preserve Governance While Eliminating Operational Drag
Consider building internally if:
- You operate 10,000+ endpoints
- Budget exceeds $2M annually
- You require strict national-security isolation
- You can sustain 24/7 staffing long-term
See roadmap guidance in the Build a SOC Step-by-Step Guide.
Outsourcing becomes strategic when:
- 24/7 coverage is inconsistent
- Alert fatigue is rising
- Senior analyst retention is unstable
- Compliance demands are increasing
- Budget predictability matters
Explore scalable solutions under Managed SOC Services.
Ask:
- Do we sustain 24/7 coverage without burnout?
- Are detections continuously tuned?
- Do we measure MTTD and MTTR?
- Can we accurately model 3-year SOC TCO?
- Are we audit-ready year-round?
If three or more answers raise concern, Managed or Hybrid SOC should be evaluated immediately.
The strongest security programs are not defined by ownership of a SOC.
They are defined by:
- Detection speed
- Response maturity
- Continuous tuning
- Operational resilience
In-house SOC offers control. Managed SOC offers scale and specialization. Hybrid SOC offers strategic balance.
If you’re evaluating your next move, explore how structured, 24/7 security operations can elevate your defense posture through our SOC Services.
Replace Structural Drag With Engineered Security Operations
Enterprise-Grade Detection Designed for Growth
Tags
About Hamza Razzaq
Hamza Razzaq is a cybersecurity professional with 10 years of SOC operations experience, specializing in threat monitoring, incident response, and SIEM-based detection across enterprise environments.