Cybersecurity Insights & Expertise
Stay ahead of evolving threats with expert analysis, industry trends, and practical cybersecurity guidance from our team of security professionals.
Featured Article
 Featured
FeaturedNCNICC-1:2025: Every Saudi Private Company Now in Scope
For years, Saudi Arabia's cybersecurity regulations were something most private companies could safely ignore. The National Cybersecurity Authority's rules applied to government bodies and operators of Critical National Infrastructure banks, energy, telecoms and almost everyone else watched from the sidelines. In January 2026, that changed completely, and most companies still do not know it. If you are ready for compliance we have NCA ECC Checklist: Score Your Readiness, No Sign-Up. The NCA rel
Hisham Mir
May 28, 2026
Latest Articles
Showing 1-12 of 89 articles
SOC 2 Compliance for SaaS: The Complete Guide
There is a moment almost every B2B SaaS company hits. A major enterprise deal is moving, an investor is circling, or a regulated customer enters procurement and then the email arrives: "Please share your SOC 2 report." If you do not have one, the deal stalls, sometimes for months, sometimes for good. SOC 2 has quietly become the price of entry for selling software to serious customers. SOC 2 compliance for SaaS means having an independent auditor attest, in a formal report, that your company's
Hisham Mir
May 25, 2026

NCA ECC Checklist: Score Your Readiness, No Sign-Up
NCA ECC Compliance Checklist
Babar Khan Akhunzada
May 25, 2026
NCA ECC: 4 Domains, 108 Controls & Compliance Explained
If you are reading about the NCA's Essential Cybersecurity Controls, there is a good chance the guidance in front of you is out of date. Most articles still describe ECC-1:2018 the original version including its control count, its five domains, and its Saudization rule. All three of those changed when the NCA released ECC-2:2024, the NCA ECC Checklist: Score Your Readiness in Saudi Arabia. The Essential Cybersecurity Controls are the NCA's foundational framework: the minimum cybersecurity requi
Hisham Mir
May 25, 2026

What Is the NCA? Saudi Arabia's Cybersecurity Authority
If you run a business in Saudi Arabia, the rules on cybersecurity changed at the start of 2026 and the change now reaches far more companies than before. The body behind those rules is the National Cybersecurity Authority, almost always referred to simply as the NCA. SecurityWall offers NCA ECC Checklist: Score Your Readiness, No Sign-Up. The NCA is Saudi Arabia's national cybersecurity regulator the single government authority responsible for setting, issuing, and enforcing cybersecurity requi
Hisham Mir
May 24, 2026

SOC 2 Compliance Checklist 2026 (Interactive, 12 Domains)
This is an interactive, use-it-now SOC 2 compliance checklist covering all 12 control domains. Tick items as you go the progress bar tracks your completion, and each domain tells you exactly what evidence auditors look for and the single most common gap they find. Nothing is saved or sent anywhere; it runs entirely in your browser. The checklist gives you the shape of SOC 2 readiness the key checkpoints in each domain. It is not the full control set; a complete SOC 2 programme spans 200+ contro
Hisham Mir
May 24, 2026

SOC 2 vs ISO 27001: Differences and Which You Need
"SOC 2 vs ISO 27001" is one of the most-searched questions in compliance and it is usually the wrong question. People type it expecting to learn which framework is better, as if one were a stronger version of the other. They are not competing tiers of the same thing. They are two different instruments, built by different bodies, recognised in different markets, that happen to cover a heavily overlapping set of security controls. The better question is not "which is better" it is "which one are
Hisham Mir
May 24, 2026
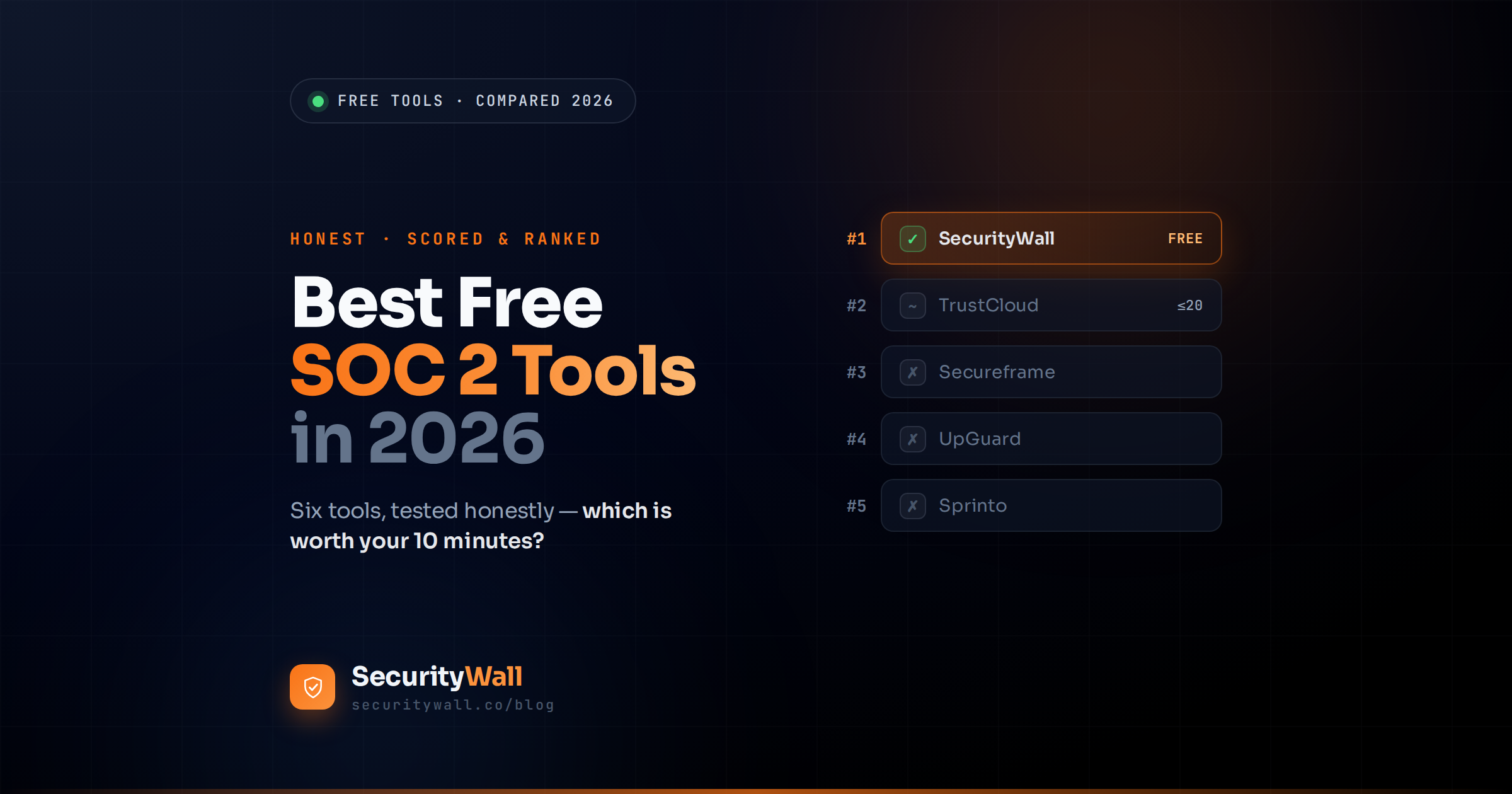
Best Free SOC 2 Tools in 2026
Most companies evaluating SOC 2 readiness tools are about to make an expensive decision. A SOC 2 programme between audit fees, tooling, and remediation routinely runs $30,000 to $100,000 in the first year, and the people researching free tools want to know where they stand before committing a dollar of it. The problem is that "free SOC 2 tool" describes a wide and inconsistent range of things interactive scored assessments, downloadable checklists, vendor-risk templates, and platform onboarding
Babar Khan Akhunzada
May 23, 2026
SOC 2 Readiness Assessment: Free Tool, Instant Score
You are about to spend $20,000 to $80,000 on a SOC 2 audit. Before you sign the engagement letter, the cheapest insurance you can buy is finding out, in advance, whether you are actually ready for it. SOC 2 audits do not refund failed attempts. Auditors do not pause their billing because your controls were not where you said they were. And the gap between "we are pursuing SOC 2" and "we are audit-ready" is, in our experience, a 4-to-6-month remediation programme not the two-week sprint most foun
Hisham Mir
May 23, 2026
Penetration Testing for SOC 2, ISO 27001 and PCI DSS (2026)
Modern SaaS, cloud, and fintech company will commission penetration tests this year. The question is no longer whether it is how many separate tests, against how many separate frameworks, and how much of the work can be consolidated. SOC 2 expects penetration testing under Common Criteria 4.1 and 7.1. ISO 27001 expects it under control 8.8. PCI DSS prescribes it explicitly under Requirement 11.4. HIPAA refers to it obliquely as "technical evaluation" under §164.308(a)(8). And in 2026, the EU's
Babar Khan Akhunzada
May 19, 2026
SOC 2 Type 1 vs Type 2 in 2026: What's the Difference
There are two SOC 2 reports. One takes 4 to 8 weeks and gives your customer a snapshot. The other takes a year and gives them a track record. The choice between them shapes your timeline, your audit cost, and most importantly whether your enterprise prospects accept the report or send you back to do the work properly. Type 1 is the snapshot. Type 2 is the track record. They are not interchangeable, they cost different amounts, they take wildly different lengths of time, and most enterprise proc
Babar Khan Akhunzada
May 7, 2026
What Is SOC 2 Compliance? Guide for SaaS Companies
A prospective customer has asked for your SOC 2 report. Your investor's due diligence checklist requires one. Procurement at a Fortune 500 has flagged that they cannot move your contract forward without it. And the question you are now staring at possibly for the first time is what does that actually mean, and how long is this going to take. SOC 2 is not a regulation. There is no government agency that fines you for non-compliance, no statutory deadline, no licence to revoke. It is also not, st
Hisham Mir
May 5, 2026
PCI DSS for SaaS and Fintech
Most SaaS and fintech companies dramatically underestimate their PCI DSS scope on first contact with the standard. The pattern is consistent: a CTO or head of engineering reviews the merchant levels, sees that their company processes "fewer than 6 million transactions a year," and concludes incorrectly that they qualify as a Level 4 merchant with a 24-question Self-Assessment Questionnaire and minimal compliance burden. Then a QSA, an enterprise customer's procurement team, or an acquiring bank
Hisham Mir
May 3, 2026